OSI is a standard description or "reference model" for how messages should be transmitted between any two points in a telecommunication network. This model is designed to interconnect computers, but is now applied in several other areas, like wireless.
” A reference model is a conceptual blueprint of how communications should take place. it addresses all the processes required for effective communication and divides these processes into logical grouping called layers. ”
The seven Layers of the OSI Model :-
Layer 7: Application Layer
Layer 6: Presentation Layer
Layer 5: Session Layer
Layer 4: Transport Layer
Layer 3: Network Layer
Layer 2: Data-Link Layer
Layer 1: Physical Layer
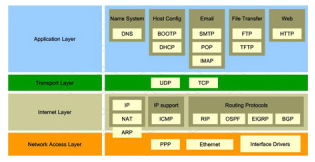
Application Layer
In this layer we have the User Interfaces, which are created by the data itself (email, file transfer, etc). This is where the data is sent and received by users. Such requests are made by applications according to the protocols used.
This layer is probably that you are more used to. You interact directly with it for example when using a program to read or send email, or communicate through instant messaging.
Protocols: BitTorrent, BGP ,BOOTP , DNS, DHCP , FTP , HTTP, HTTPS, IMAP, LDAP , MIME , NetBIOS , NNTP, NTP, POP3 , RADIUS , RDP, RTP, RTSP , SSH , SIP , SMTP, SNMP, SMB, Telnet, TFTP,
Presentation Layer
At the Presentation layer (Layer 6) data is first converted into a form that can be sent over a network. At this layer data is compressed and decompressed and encrypted or decrypted, depending on which direction it's traveling.
Protocols: SSL, TLS.
Devices: Gateways (translating protocols between different networks).

Session Layer:
This layer deals with communication between two devices. For example: when the user goes to a website, the user’s computer must open a session between itself and server hosting the website, thus allowing the user to receive the website in the first place. The same goes for any sort of communication, ie VOIP etc.

Function: start, manage and terminate sessions for the presentation layer, eg TCP sessions.
Transport Layer:
This layer manages the end-to-end control (for example, determining whether all packets have arrived) and error-checking. It ensures complete data transfer.
This layer is responsible for resending any packets that do not receive an acknowledgment from the destination address. It's also responsible for any problems that are associated with fragmentation of packets.
Network Layer :
This layer handles the routing of the data (sending it in the right direction to the right destination on outgoing transmissions and receiving incoming transmissions at the packet level). The network layer does routing and forwarding.

Data Link Layer:
The Data Link layer (Layer 2) is responsible for sending data to the Physical layer so that it can be put onto the "wire" or network media. The Data Link layer is subdivided into two other layers: the Logical Link Control (LLC) and the Media Access Control (MAC) layers. The LLC connects the Data Link layer to the higher-level protocols such as IP at the Network layer. The MAC layer connects the Data Link layer to the physical connection and provides the MAC address. The Data Link layer also defines the technology that is used for the network. This layer can also perform checksums, which are calculations that the system uses to make sure that packets are not damaged in transit.
Physical Layer:
The Physical layer (Layer 1) defines the physical characteristics of the network such as the type of cable that must be used as well as the voltage that will be used to transmit data through the network. Since the Physical layer defines these characteristics, it also establishes the topology of the network. Many standards are defined at this layer, such as the IEEE 802.3 standard for Ethernet as well as the IEEE 802.5 standard for Token Ring networks.

